Executive Summary
A new campaign is circulating online, impersonating the official El Al Israel Airlines mobile application and using sponsored-style ads to lure users into installing a fake app.
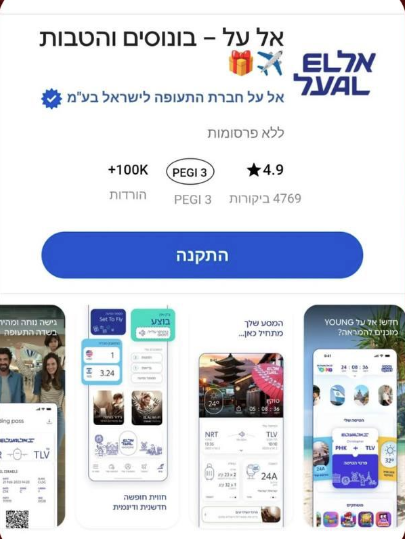
The ad presents a highly convincing interface, including:
* Official branding and logo
* App store-like layout (ratings, downloads, PEGI label)
* A prominent “Install” (התקנה) button
This creates a false sense of legitimacy and trust.
Attack Flow
* Download a malicious APK / profile
* Or enter personal and payment details
Indicators of Compromise (IOCs)
* Fake app distribution outside official stores
* Use of Hebrew UI mimicking trusted Israeli brands
* Overly generic install interface not tied to Google Play / App Store
* Suspicious hosting domains (not shown but implied from flow)
Key Risks
* Malware infection on mobile devices
* Credential theft (email, passwords, travel accounts)
* Financial fraud via stored payment methods
* Brand abuse is damaging trust in El Al
Why This Works
* High trust in national airline brand
* Familiar app store UI patterns
* Mobile users tend to act quickly without verifying the source
* Ads increase perceived legitimacy
Recommendations
For Users
* Only download apps from Google Play / Apple App Store
* Verify publisher name before installation
* Avoid clicking “Install” from ads or pop-ups
For Organizations
* Monitor for brand impersonation campaigns
* Work with platforms to remove malicious ads quickly
* Educate users about fake app distribution risks
AI Security Advisor
Powered by Gemini
Get AI-powered security recommendations tailored to this specific threat — including risk assessment, detection guidance, MITRE ATT&CK mapping, and actionable remediation steps.
Sources
Protect Your Organization
Monitor CVEs, scan for vulnerabilities, and get real-time threat alerts — all in one platform.
Get instant alerts on Telegram
Join our public channel for real-time critical CVE alerts.
Follow @vulnios