Executive Summary
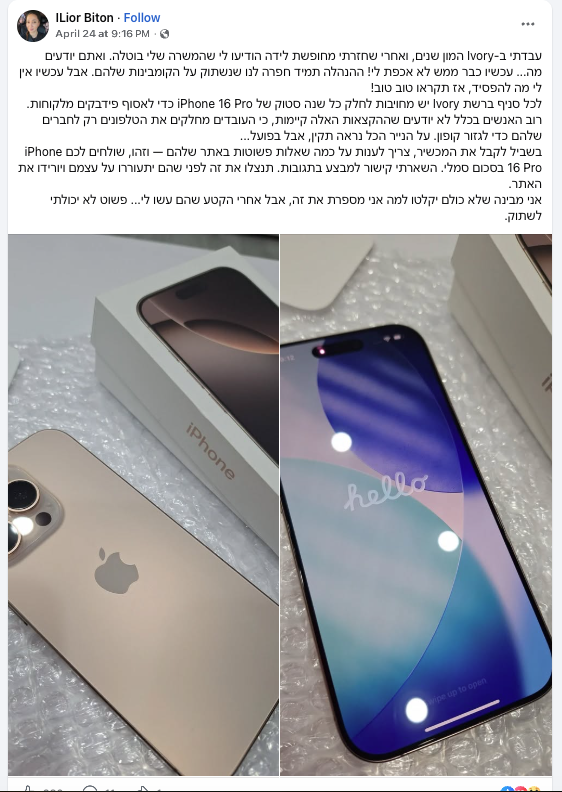
A phishing campaign is actively targeting users via Facebook-sponsored content, redirecting victims to a malicious website that impersonates Ivory and offers discounted iPhone 16 Pro devices.
The campaign uses a Facebook redirect link (l.facebook.com) to mask the final destination and increase user trust, leading to the domain:
* Malicious domain: top-rewards[.]online
Attack Flow
* Credit card details
* Personal information
Indicators of Compromise (IOCs)
* top-rewards[.]online
* Facebook redirect pattern: l.facebook.com/l.php?...
* Unrealistic discounts on high-demand products (iPhone 16 Pro)
* Urgency messaging (“limited offer”, “act now”)
Key Risks
* Financial fraud – direct theft via payment details
* Identity theft – collection of personal information
* Brand abuse – impersonation of trusted retailers (Ivory)
* Trust bypass – leveraging Facebook infrastructure to appear legitimate
Why This Works
* Users trust Facebook-hosted links
* Strong brand impersonation increases credibility
* Mobile users are less likely to inspect full URLs
* Psychological pressure drives fast decisions
Recommendations
For Users
* Avoid clicking on promotional links from social media without verification
* Always navigate to official websites manually
* Never enter payment details on unfamiliar domains
For Organizations
* Monitor for brand impersonation campaigns
* Implement threat intelligence feeds to detect malicious domains
* Educate users about social media phishing risks
AI Security Advisor
Powered by Gemini
Get AI-powered security recommendations tailored to this specific threat — including risk assessment, detection guidance, MITRE ATT&CK mapping, and actionable remediation steps.
Sources
Protect Your Organization
Monitor CVEs, scan for vulnerabilities, and get real-time threat alerts — all in one platform.
Get instant alerts on Telegram
Join our public channel for real-time critical CVE alerts.
Follow @vulnios