Executive Summary
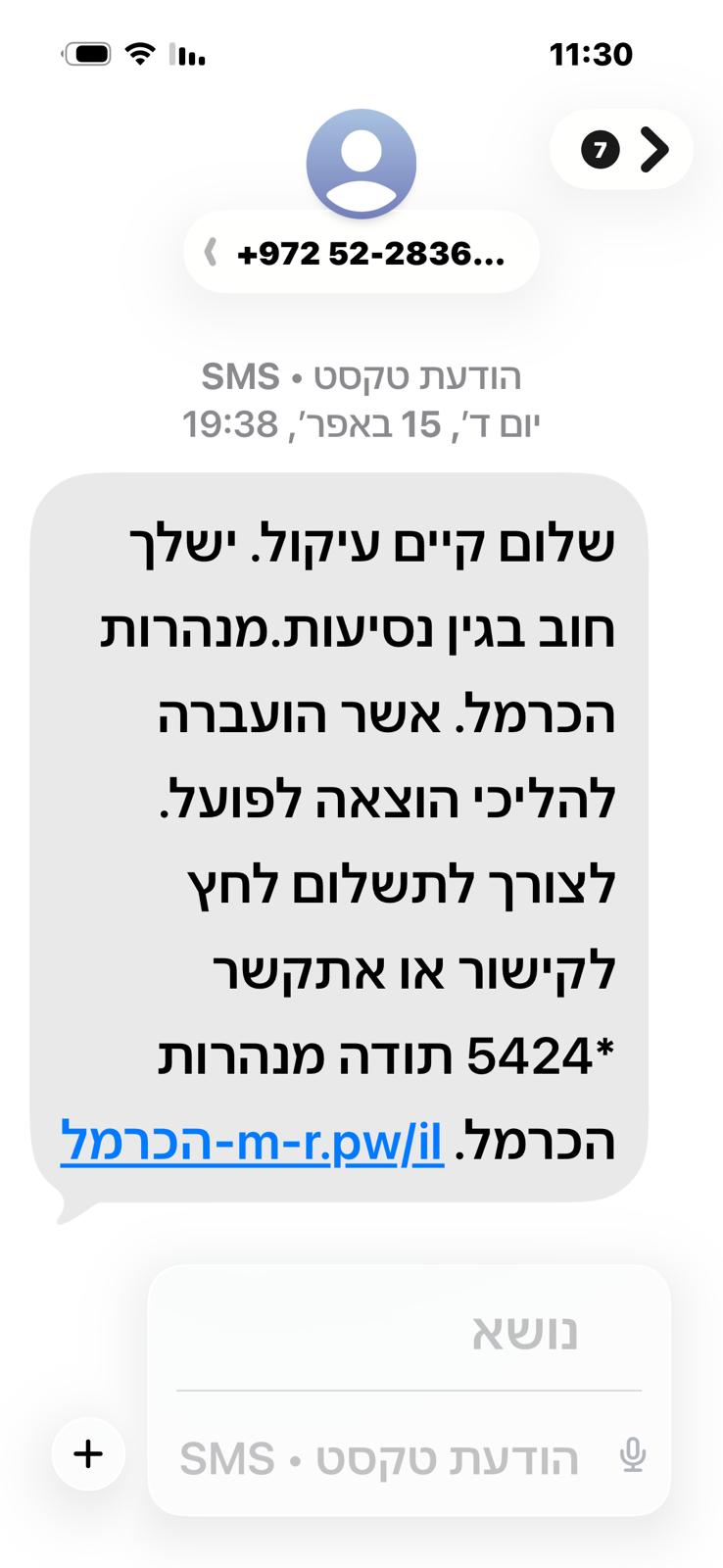
A new phishing campaign is targeting Israeli users via SMS, impersonating the Hacarmel Toll Road.
The message claims the recipient has an outstanding toll payment and pressures them to act immediately by either paying via the provided link or contacting the support number.
Indicators of Compromise (IOCs)
* Malicious domain: hxxps://הכרמל-m-r[.]pw/il
* Phone number: +972 52-2836XXX
* Use of urgency and financial pressure
* Generic messaging without personalized details
Attack Flow
* Credit card details
* Personal information
Key Risks
* Financial theft via stolen payment details
* Identity theft through personal data collection
* Follow-up attacks using harvested information
Why This Works
* SMS messages bypass many traditional email security controls
* The use of a trusted brand (Hacarmel) increases credibility
* Shortened / unfamiliar domains reduce user suspicion
* High-pressure language pushes users to act without verification
Recommendations
For Users
* Do not click on suspicious links in SMS messages
* Verify payments only via official websites or apps
* Avoid calling numbers provided in unsolicited messages
For Organizations
* Implement SMS phishing awareness training
* Monitor for brand impersonation campaigns
* Consider mobile threat defense (MTD) solutions
AI Security Advisor
Powered by Gemini
Get AI-powered security recommendations tailored to this specific threat — including risk assessment, detection guidance, MITRE ATT&CK mapping, and actionable remediation steps.
Sources
Protect Your Organization
Monitor CVEs, scan for vulnerabilities, and get real-time threat alerts — all in one platform.
Get instant alerts on Telegram
Join our public channel for real-time critical CVE alerts.
Follow @vulnios